File Shield + Flight Recorder: How Yeet Stops the Trivy Attack Pattern with eBPF
A compromised GitHub Action exfiltrated credentials from 10,000+ CI/CD pipelines. That’s the overview of last month's Trivy attack.
We fed the incident report into Yeet and generated a working kernel-level defense.
Let’s get into it
The Trivy team knew there was a credential leak, but they weren’t able to completely contain it fast enough. With working credentials in hand, TeamPCP had an open door into the aqua-bot service account.
Then a whole bunch of terrible stuff happened.
What’s interesting is that this is the modern attack trend: Targeting tools and infrastructure we all trust.
The other interesting point is that this could have been prevented using eBPF (What is eBPF?)
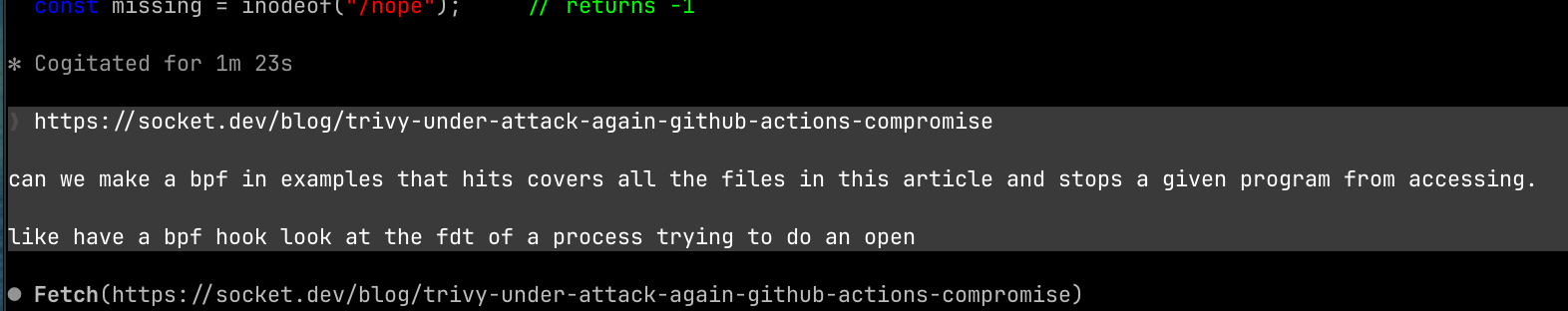
We put an article on the Trivy attack into the Yeet AI engine and asked it:
“Can we make a bpf that covers all of the files in this article and stops a given program from accessing it?”
Introducing File Shield
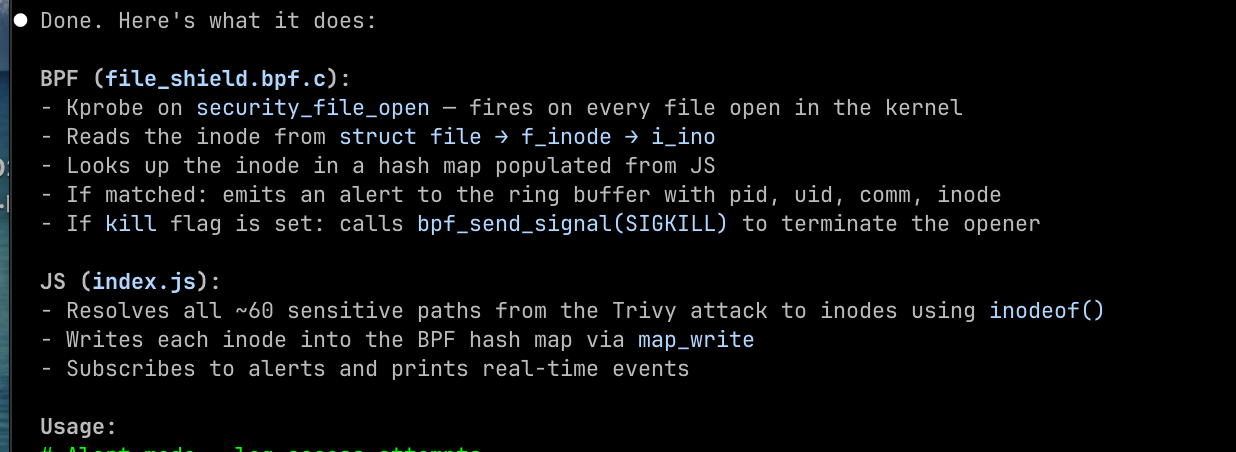
File Shield is an eBPF program that fires on every file open, at the kernel level. Not at the application layer, not via a policy engine sitting in userspace. At the exact moment the kernel processes the open() syscall.
Get early access to Yeet
Join the waitlist and be first to know when we launch.
This one used the article as context to resolve all ~60 sensitive file paths from the Trivy attack to their inodes, writes those inodes into a BPF hash map, and watches. When any process tries to open a matched file, Yeet emits an alert with the process ID, user, and command. If enforcement mode is on, it sends SIGKILL. The process doesn't get an error. It gets terminated.
The Trivy attack read ~/.aws/credentials, service account tokens, and similar paths that exist on essentially every CI/CD runner. File Shield makes those paths invisible to any process you don't explicitly trust, including an agent runtime that's been compromised without your knowledge.
This is what "kernel-level" actually means in practice. It's not a wrapper. It's not a middleware. The block happens before the file descriptor is returned. There's no userspace path that routes around it. And it’s not just files, this configuration works for the entire network (IPs, URLs, Geos, etc.)
And when enforcement isn't enough: Introducing Flight Recorder
File Shield answers the question: what if we could have stopped it?
The Flight Recorder answers the question that comes after every incident: what exactly did it do before we caught it?
When an AI agent connects over SSH, Yeet's Flight Recorder correlates every syscall, every exec, every open, every connect, every process spawn, back to the session that initiated it.
Structured, queryable, tamper-proof. The agent operates in userspace. The recording happens in kernel space. Those don't overlap, which means the agent can't see, modify, or clear its own audit trail.
Not only does this open up a greater trust space for agents, but it stops new types of agentic attacks, before they happen.
Together, File Shield and the Flight Recorder form a complete loop. File Shield prevents the Trivy attack pattern from completing. The Flight Recorder tells you everything the agent touched on its way to the file it never got to open. One stops the breach. The other gives you the forensics to understand it, and prove to your compliance team that your controls actually worked.
Pump the brakes. What is Yeet?
Did I just show you that you can use the Yeet AI to build you a custom security tool based on a news article?
I did.
Yeet uses a unique combination of eBPF + JavaScript + AI to create scripts that can see and manipulate data in your infrastructure, from file access to syscalls to SSH sessions.
Yeet also owns the ports where data from the network comes into the computer. It can look through millions of packets per second, analyze them, and stop any of them before they enter.
This is an exciting new era for technology, and we can’t wait to see what you’re going to build with it.